As the Senior Vice President of Product, I am thrilled about the latest release in Parallels platform – Parallels Browser Isolation (PBI).
In this post, I’d like to emphasize the importance of Parallels Browser Isolation and how it...
The advantages of Desktop as a Service (DaaS) for MSPs.
As organizations strive to maintain operational continuity, optimize their resources, and secure sensitive data, Desktop as a Service...
DaaS is a cloud-based model where a third-party provider hosts and delivers virtual desktops to users. Unlike traditional VDI, which requires organizations to manage their own on-premises...
The foundations of a successful MSP business model are stability, predictability, and reliability.
This encompasses vendor partnerships and continuity in delivering managed services to...
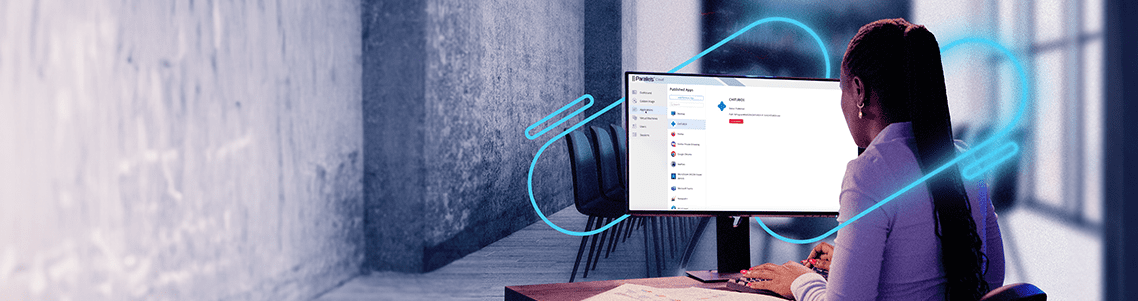
Remote Desktop Services (RDS) by Microsoft has long been a game-changer in remote computing, offering a gateway to seamless application and desktop access.
However, as technology evolves, so do...
In the ever-evolving landscape of the modern workplace, the traditional office setup has undergone a remarkable transformation.
With the ascent of mobile work environments, employees are breaking free from...
How do Apache Guacamole and Parallels Secure Workspace compare?
Apache Guacamole and Parallels Secure Workspace offer a built-in RDP to HTML5 gateway, so it is no wonder these two solutions are often compared. In this blog post, I’ll...
MSPs often adopt a multi-cloud strategy, leveraging a mix of public cloud vendors like AWS, Azure, and Google Cloud to deliver a diverse range of managed services. These services include virtual applications and desktops,...